Oryx Embedded, a member of the ST Partner Program, published benchmarks showing the STM32H5 is up to 169% faster than an STM32F4 in cryptographic computation, thus making networking and security solutions more accessible to embedded systems engineers. In a nutshell, Oryx Embedded offers developers a way to work more efficiently on a microcontroller instead of having to adopt something much costlier, like a microprocessor. Indeed, working with protocols like TCP or STP and common encryption mechanisms like SSH, SSL, or TLS is straightforward on a Unix kernel because there are already a lot of solid implementations. Unfortunately, the same isn’t true on microcontrollers. Oryx Embedded remedies this challenge by delivering stacks and libraries to developers working on an RTOS.
What security on microcontrollers means today
It’s a way to care for end users

Microcontrollers don’t simply process more data but also deal with more sensitive information that can compromise a user’s location, private information, banking data, etc. Consequently, hackers are significantly more motivated to compromise systems, and vulnerabilities are vastly more damaging than they would have been a few years ago. It’s why ST keeps working on STM32Trust initiatives, such as Secure Manager, a turnkey solution at the system level that simplifies the implementation of critical safeguards like a root of trust. By offering a ready-to-use system, like our new STM32H5 Development Kit that supports Secure Manager, we aim to motivate developers to adopt tighter security measures in their applications.
It’s a way to democratize machine learning at the edge
Security is also a growing concern because of the new popularity of machine learning applications at the edge. Indeed, a failure to protect the RAM could lead a hacker to modify the neural network algorithm to skew results, unbeknownst to the users or developers. Similarly, an insecure network could lead to a man-in-the-middle attack that intercepts data, which could have pernicious effects on training sets or inferences. Even worse, a rootkit could compromise a system at the boot level, blocking over-the-air updates meant to update a neural network. While protecting networks and boot loaders isn’t new, machine learning applications come with new risks that make their safeguard even more critical.
It’s a way to innovate
One consequence of the new trends shaping embedded systems is that security requirements are more stringent, and government regulators are paying more attention and even mandating certain safeguards. The challenge is that developers must quickly learn the underlying mechanisms of complex security features to gain the expertise needed to implement the right protections for their applications. Put simply, some are asked to understand concepts that take years to master, which is often unrealistic.
Moreover, moving to a microprocessor and embedded Linux is often not commercially viable, but implementing security solutions from scratch on a microcontroller is a dark alley that can tragically slow down a release to market. Too often, people familiar with the ease of use of security implementations on PCs or Embedded Linux drastically underestimate the work needed on a microcontroller because it demands complex optimizations to run on resource-constrained hardware. Indeed, developers must deal with the technical realities of an RTOS on top of managing smaller memory capacities and lower computational throughputs.
Why Oryx Embedded Benchmarked the STM32H5 and what can developers expect
STM32F4 vs. STM32H5
It’s precisely for all those reasons that Oryx Embedded published an extensive list of benchmarks comparing the STM32H5 and the STM32F4. The tests ran multiple encryption and decryption schemes and various algorithms, from the classic AES to MD5, 3DES, RSA, Diffie-Hellman (up to 2048 bits), and more. When using the AES scheme, the new mainstream microcontroller is at least 105% faster and often about 150% quicker in many cases. Similarly, asymmetrical schemes like RSA benefit from a significant performance boost of roughly 35% to 40%, thanks to a higher frequency and better memory management. Hence, simply moving from an STM32F4 to an STM32H5 will tremendously impact existing applications that use Oryx Embedded software.

Software vs. Hardware acceleration
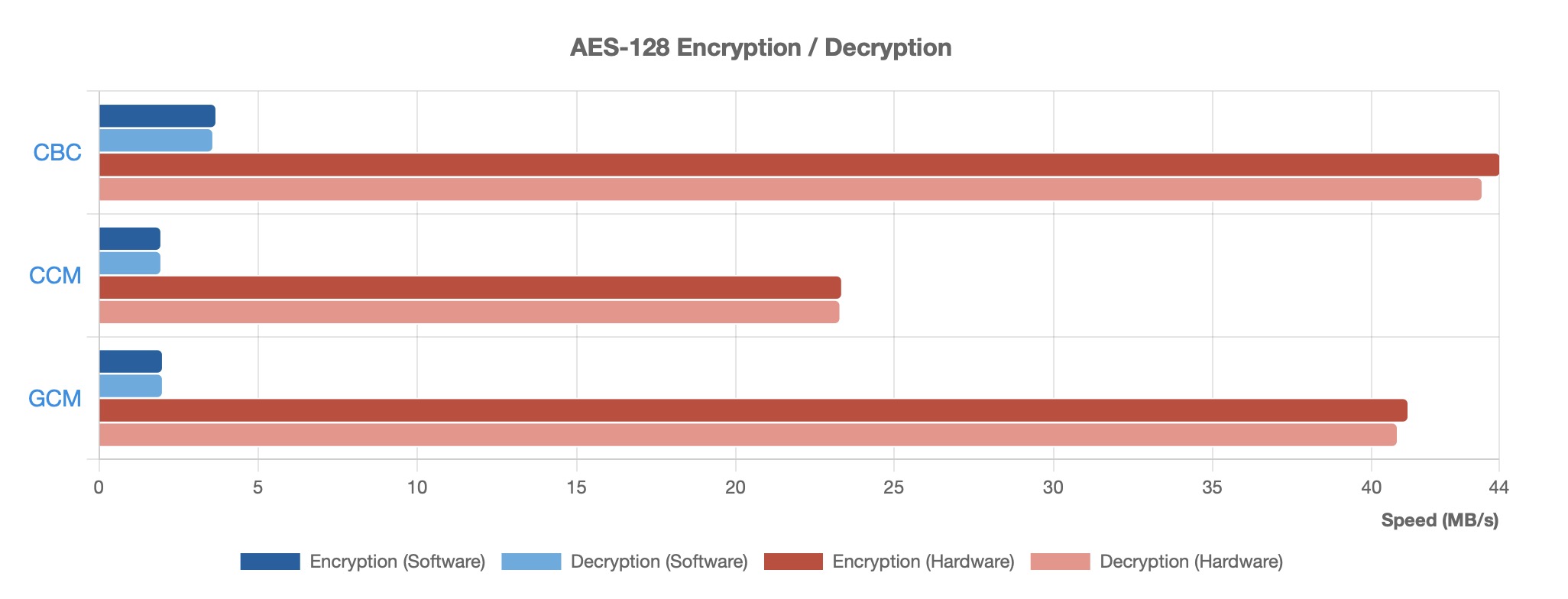
All the benchmarks above compare software implementations, meaning they don’t even take advantage of the fact that the STM32H5 has a hardware accelerator for symmetric (AES) and asymmetric (ECDSA, ECDH, RSA, etc.) key algorithms. Indeed, Oryx Embedded published another set of tests comparing the software implementations against our hardware acceleration. For instance, using our hardware accelerator to encrypt or decrypt data using AES-128 is more than 10x faster. Similarly, while using a software implementation takes 293.3 ms to compute a signature using RSA 2048 bits, it takes only 48.5 ms with our hardware IP. Consequently, it opens the door to new applications that couldn’t tolerate the previous long wait time.
Creating secure applications from the start
Oryx Embedded has been releasing stacks and libraries for nearly all STM32s, enabling developers to work with familiar protocols and security technologies. However, the ST Authorized Partner has been emphasizing the performance of the STM32H5 because the MCU also includes an Ethernet module, thus opening the door to the creation of gateways, web servers, and remote systems with little to no external modules needed. In practical terms, it means developers can open parallel connections without slowing their system to a crawl or accelerating handshakes to create a smoother experience for users without compromising security.
Interestingly, the ST Partner Program member explained that, at first, its teams used our Hardware Abstraction Layer to accelerate developments. Then, as Oryx Embedded gained experience, it customized even the lowest levels of its code to improve performance and portability. By writing bare metal code, the company became more familiar with our architectures, thus porting its libraries and stacks to new STM32s faster. Today, Oryx Embedded provides GPLv2 open-source versions of its stacks and evaluation versions to help teams get started, regardless of their expertise level. In a nutshell, we are thrilled to work with Oryx Embedded because they share our desire to make security more accessible to all embedded system developers.
